Guest blog post by Aleksander (@aleksanderrr_) and Intel Inquirer (@intel_inquirer)
STRAVA is one of the worlds’ most popular social media platforms, used by more than 50 million people to monitor and share their cycling/running exercises. Since the platform’s initial launch in 2009, it has recorded more than 4 billion activity uploads and throughout the COVID-19 pandemic, the number of new users have soared as people have turned to alternate forms of exercise around their local vicinity due to gym closures and other lockdown measures.
In this blog post, we’ll take a look at the four main sections on Strava’s desktop platform, and how they can be leveraged in online investigations. But before we dive into the details of each of the functions, let’s start with the basic functionality of the site.
In order to access the Strava desktop platform, one has to create a user for the platform. This can either be done utilising Facebook, Google, Apple or an email (we recommend using a sock puppet for OSINT investigations). By creating an account, you are granted access to the platform and can freely use all of the search functionalities described in this blog post.
However, the privacy settings applied by your person of interest ultimately decides how much information you can extract from their profile.
Athlete Search
Strava allows us to look up other users on the site by their first and last name, which takes us to their main profile on the platform. These often provide us with a profile photo of the individual which we can use for identification and for cross referencing with other platforms, to confirm further social media activity/profiles.
Depending on the privacy settings, we will in most cases also get an overview of all of the particular users’ activities since they joined the site, including maps of where they have exercised. For the purpose of intelligence gathering, these stats can provide unique insight, not only giving us an idea of where they live, but also about their exercise routines, work pattern, deployments and travels out of the country.
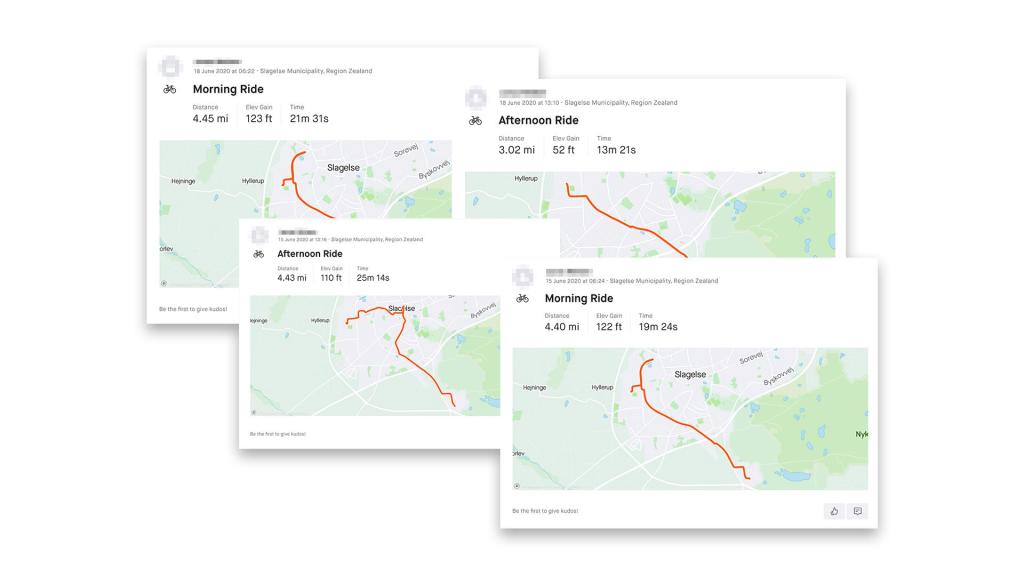
Notice the users’ start and endpoint, as well as the date stamps on the route in the images above. If you’re thinking that it looks a lot like someone taking their bike to work at the same time every morning you’d be right on the money. If we were to look up the endpoint on Google Maps, we would find that this particular user works at the Antvorskov barracks, home of the Royal Danish Army’s cavalry unit.
Simply by looking at the user’s main profile, we have established that the person is likely an employee at the barracks, possibly even in a military role, and at which times the person starts and finishes work. And these pieces of information can be further scrutinized and compared to other social media platforms such as LinkedIn, Facebook and local whitepages.
Groups
Reviewing the person’s followers/following can provide us with insight into their friends, co-workers, training partners and clubs. As STRAVA is both a personal exercise platform and a community, it allows users to upload photos with friends, and even joint exercise activities, and these breadcrumbs can lead us to other breadcrumbs which we can follow, such as a potential gym membership in their local area, cycling tournaments, and running marathons.
Segment Search
Another great feature on STRAVA, is the ‘Segment Search’ and ‘Segment Explore’ functions, which allow us to find popular user-generated running and cycling routes in a specific area.
One type of investigation, where these functions can prove particularly valuable, is when we are looking for foreign military personnel. Although soldiers are regularly on patrol or participating in exercises, the often months-long deployments equals a lot of downtime spent on keeping fit. This is something which we can exploit.
Let’s take a closer look at Tapa, Estonia, where NATO’s ‘Enhanced Forward Presence’ force in Northern Europe has been stationed since 2016, following Russia’s invasion of Crimea.
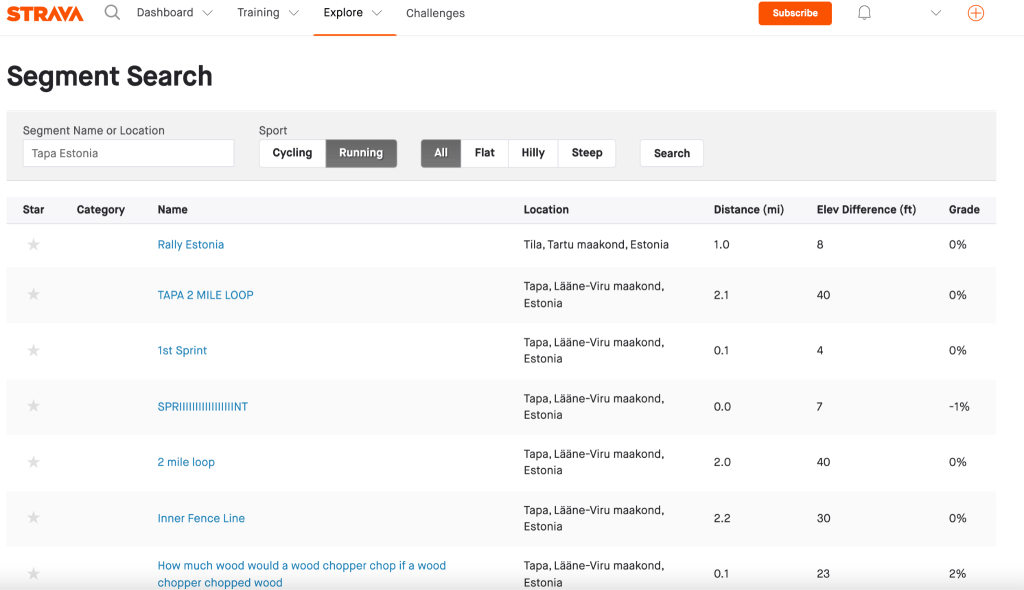
The location of the NATO force is by no means a secret, but looking at the routes in the area, there are a couple of odd ones that stick out. Although “How much wood would a wood chopper chop if a wood chopper chopped wood” or “TAPA DAPPER, TARMAC & DIRT SLAPPER 1 Lap” sounds intriguing, let’s focus on one called “Sprint to the Gd room”. According to the British MOD’s military terminology (thanks, @rag_sec!), GD can mean either of the following things:
- General Defence
- General Duties
- Graphic Display
- Ground Defence
- Guard
- Gun Director
If we look at a map of the base, we can rule out most of the possible meanings as both the starting- and endpoints are either inside the fence perimeter, the lack of antennas and cables coming out of the building and the fact that soldiers are able to freely use it for exercising purposes. The most likely scenario is therefore, that the building is housing a General Duties room. At this point we have identified an interesting route within the compound.
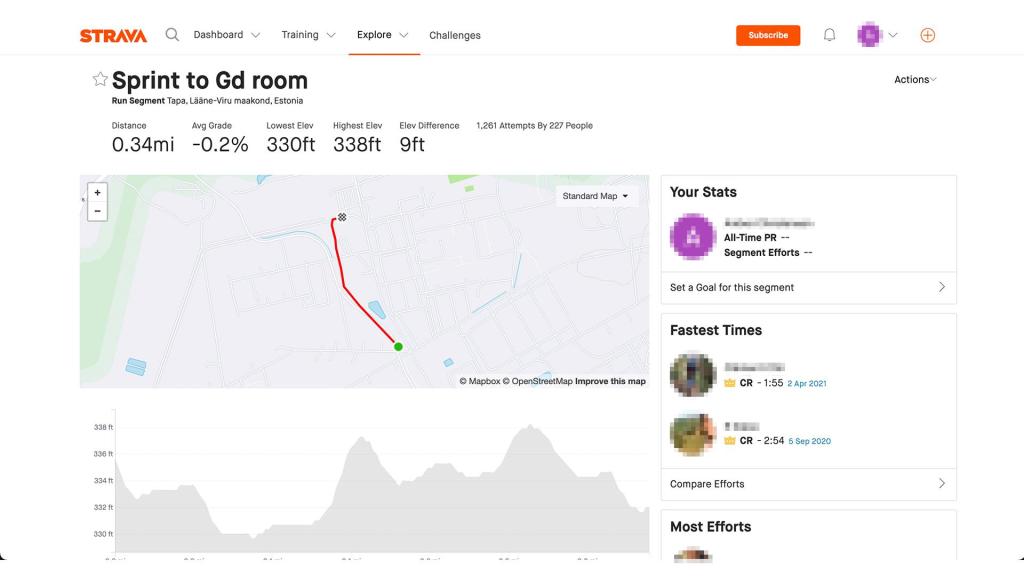
Let’s look at the other route. This one is called “Inner Fence Line”, and sure enough, if we switch the default map with the Satellite Map (marked by the yellow box) we now also have a nice overview of where the compound’s perimeter is. This could naturally be done manually by looking at the base in something like Google Earth Pro, but as bases will often have different layers of external security layers, this route makes it easier for us to differentiate between these and map out the compound.
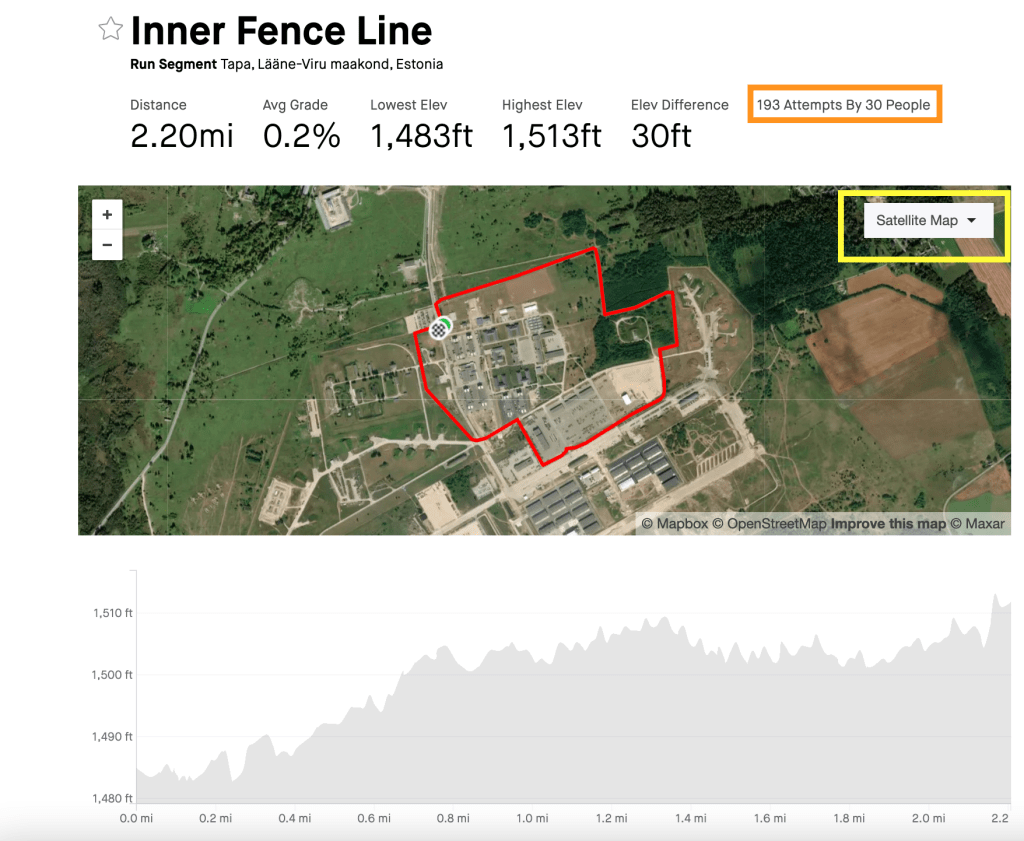
Just above the map switch, we can also see a list of users who have attempted to complete the route – and whom for us as investigators present a whole new array of pivot points in our investigation. But that isn’t all, the Segment Search and Explore functions have to offer
Clicking on the route will also give us a leaderboard of the route in question. Here we can see who has done the best times and we can use this information to map when a particular service member has been deployed to any given base.
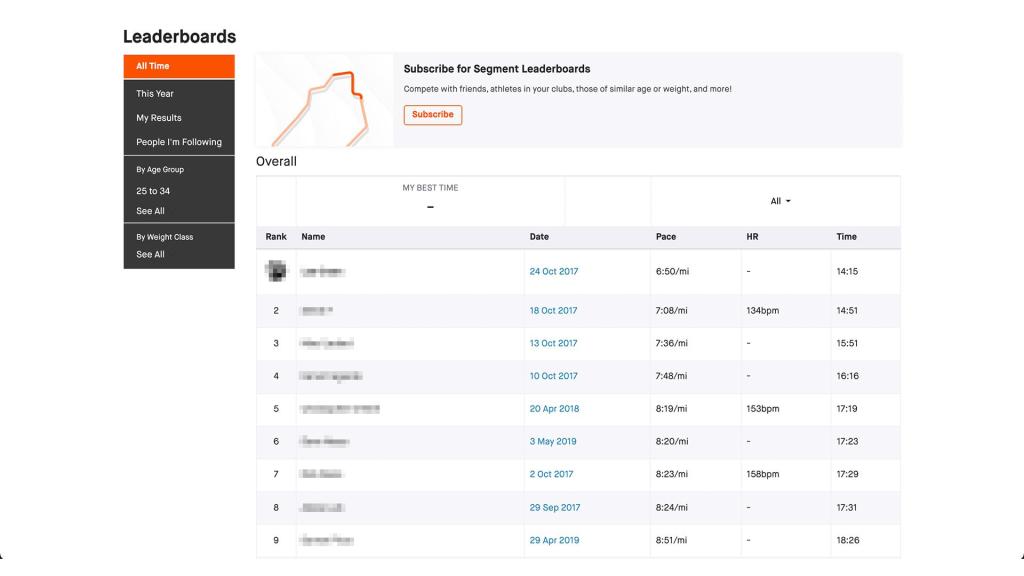
Simply by looking up routes in the area of a NATO base, we now have a piece of information about the compound which can help us identify other buildings within the compound, as well as information on runners that have completed laps within the area.
Other Resources
We hope that this short blog post has provided you with new insight into how the data aggregated by STRAVA can be implemented in your own investigations. Aware Online have also shared insight into how Strava can be used to find witnesses at any given time and place, and is a great read for those who work on missing persons or crime related investigations.
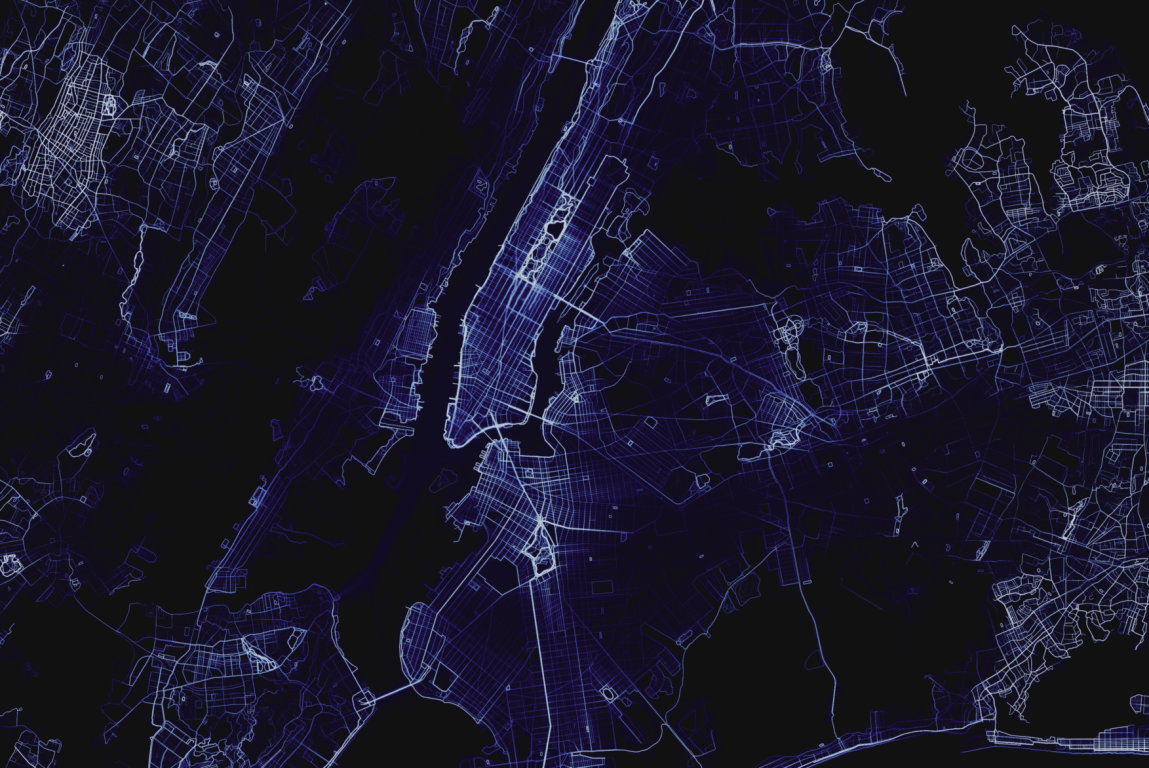
Bellingcat has also released a great article discussing how STRAVA’s heat maps can be used to view military personnel activity and movements in secret military and detention sites, which can have national security implications.
The amount of information that we are able to extract from this platform certainly makes it one you don’t want to ignore in your investigations.
Happy hunting and remember to stay OSINT curious!