
What are certificates?
Everybody on the internet uses certificates, or public key certificates, whether you are aware of it or not. Certificates are documents that can provide proof of an identity, for instance a web server that is claiming its identity to your browser. These public keys can be used for encrypting data that is sent via, for instance, a connection over HTTPS but they are also used for proving that the server you are reaching is the same server that is listed in the certificate. When a certificate checks out and the connection is encrypted, you are usually served a little green lock in your browser nowadays.

If a different server on a different URL would serve your browser the same certificate, your browser will show a warning that the connection can’t be trusted, warning you that the identity of the server in question might be incorrect. Since certificates are provided by a certificate authority and usually have checks in place to prove identities, this is an extra layer of security used to secure communication and mitigate against other types of fraud.
What is certificate transparency?
Certificate transparency was developed after the certificate authority DigiNotar was compromised in 2011. During the time that DigiNotar was compromised, there were 531 certificates issued for several different domains, among them some high profile companies like Google, Microsoft, and Yahoo! There was a need to check the certificates that were issued by the Certificate Authorities (CA), so people decided to publicly share the new certificates that were issued by a CA. By sharing all the logs publicly, companies, CAs, and browser would be able to check for the validity of the issued certificates and block whatever was deemed necessary.
What can you find inside certificates?
A certificate that is used on the internet has a fixed set of fields that are described in the X.509 standard. There are multiple interesting fields, but some of the more interesting ones are:
| Serial Number | A unique identifier for the certificate |
| Subject Common Name | The URI of the server it was assigned to |
| Subject organizationName | The company it was issued to |
| X509v3 Subject Alternative Names | Other URI’s or server names that can use this certificate |
Some of these fields can be used to find more information on a target. Whether you are performing a red team assignment, a security assessment or need to find company related information for an investigation, it can be used for all these purposes. Let’s have a look at each of these fields to see what we can do with it.
Common Name
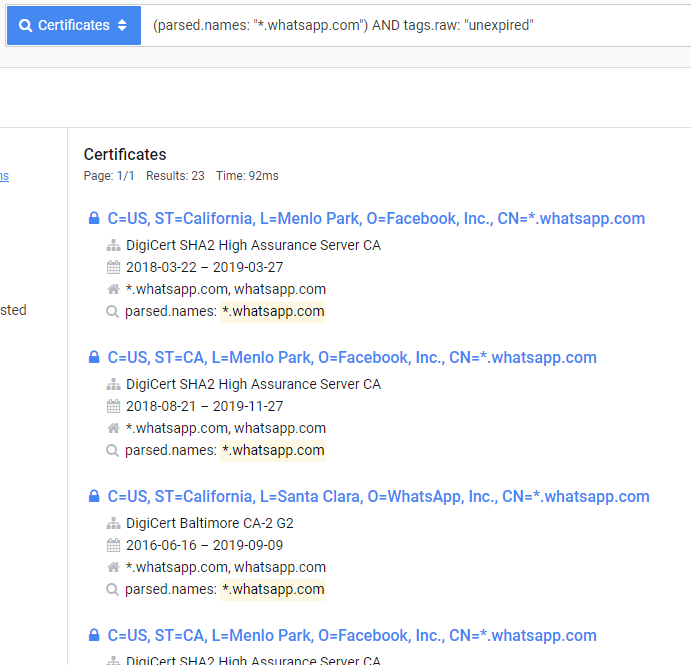
By searching for the domain name within the certificates in tools like Shodan.io or Censys.io, it is not uncommon to find multiple servers that use the same certificate. One reason is that a lot of companies use ‘wildcard certificates’, in which multiple different servers or websites can use the same certificate, as long as they are hosted within the same domain. This is possible by stating in the ‘Subject Name’ that a certificate is usable by all the sub domains of that domain it is issued to. They do that by using a wildcard “*” character like this example: *.whatsapp.com.
To query this in Shodan, you first have to create and account, because the queries use what are called ‘filters’ and everything that goes a bit deeper than a simple IP address is done by filters. Good news, even the free account is good enough to do all the things that follow. After creating an account, simply go to https://shodan.io and fill in the following in the search field or click here to go there directly:
ssl:"*.whatsapp.com"
Shodan doesn’t have a lot of options to search for specific pieces of information within a certificate, so the domain names will have to be queried via the basic “ssl” filter. To query the same in Censys, go to https://censys.io/certificates and fill in the following or click here to go there directly:
parsed.names: "*.whatsapp.com"
What is returned is a list of servers that presented a certificate that is valid for anything in regards to ‘*.whatsapp.com‘. Since Censys also shows expired certificates by default, you can select the option ‘unexpired’ in the list with tags, or manually extend the query like this or click here to open it:
(parsed.names: "*.whatsapp.com") AND tags.raw: "unexpired"
Serial Number & Fingerprint
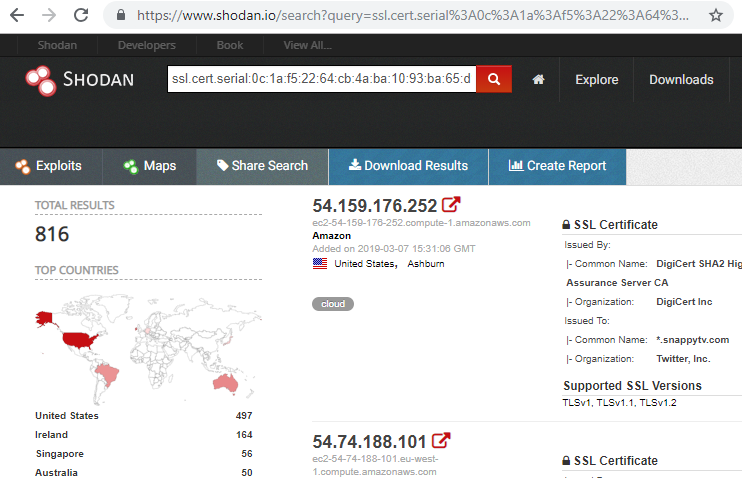
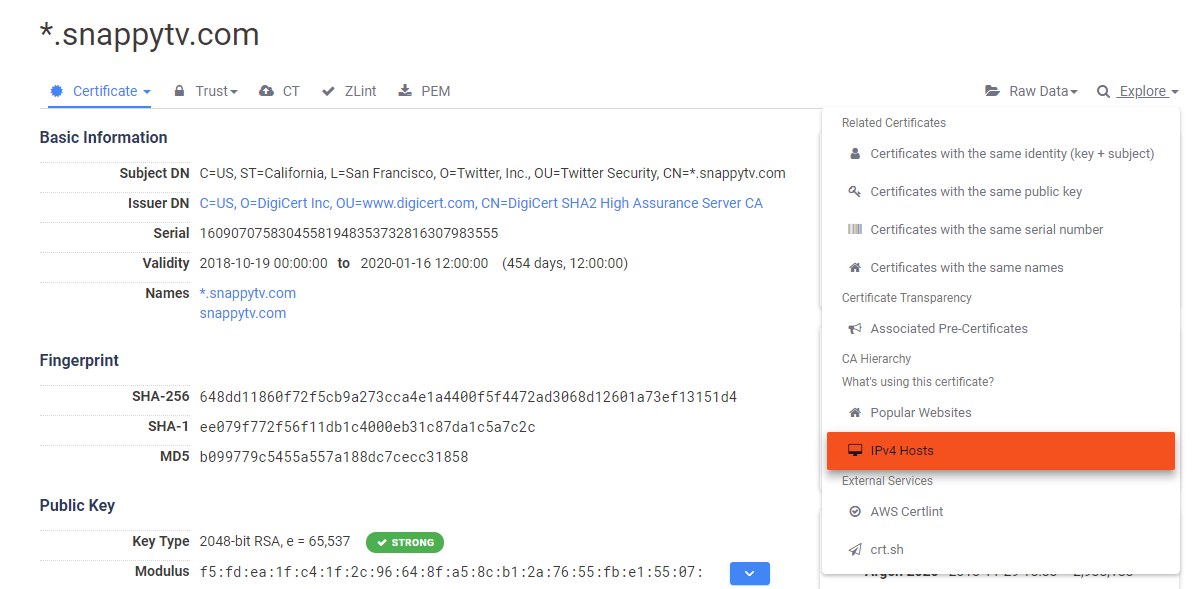
Every certificate is unique also has a serial number and can have specific fingerprints (in SHA256, SHA1, and/or MD5 hash formats). When a certificate is found, it is also possible to pivot from there and query sites like crt.sh, Shodan or Censys for websites that use this particular certificate. Let’s have a look at a certificate used by the domain snappytv.com. The latest certificate when writing this article was found here: https://crt.sh/?id=950002587
It has the following properties:
Serial number:
0c:1a:f5:22:64:cb:4a:ba:10:93:ba:65:d1:df:94:c3
Fingerprint in SHA256: 648DD11860F72F5CB9A273CCA4E1A4400F5F4472AD3068D12601A73EF13151D4
We can find related servers by feeding the serial number into Shodan, by using with the ‘ssl.cert.serial‘ directive:
If we want to do the same in Censys to find out what is in that data set and filter out all the certificates that are not valid anymore, we can query in two different ways. The first one
is to query by using the serial number, like we did in Shodan. There’s only one caveat, you need to convert the long hexadecimal serial number to a decimal format before using it in Censys. After that, it can be found via the query, that leads to the same certificate (or click here):
parsed.serial_number: 16090707583045581948353732816307983555
The second option is to use the ‘fingerprint’ that we found. The query to run is as follows (or go there directly via this link):
parsed.fingerprint_sha256: 648DD11860F72F5CB9A273CCA4E1A4400F5F4472AD3068D12601A73EF13151D4
When looking at the certificate alone, you might also wonder whether you can see which servers are sing that certificate, or maybe whether they are located in multiple countries. In Censys the easiest way to do that is click on the ‘explore’ button on the top right and select the option ‘IPv4 Hosts’ which will give back a list of servers that are using or have been using this particular certificate.
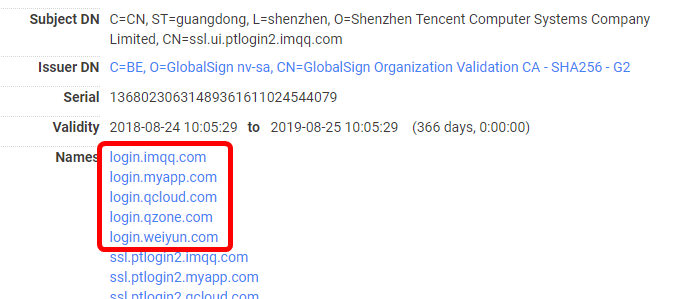
Subject Alternative Name
Besides the URL or server name a certificate was assigned to, it is possible to use a certificate for multiple domain names. It is common to see other domain names pop-up in the lists with ‘Alternative Names’, therefore giving you a pivot point for further investigations. If the certificate is also used for internal communication it is even possible that internal server and domain names show up here. This can give an even better insight into the internal infrastructure of a company, helping with the recon stage in (for instance) a penetration test, or even find different businesses that are connected to the target.
A good example of it can be seen in this certificate that was issued for the domain ‘ssl.ui.ptlogin2.imqq.com‘, where different domains can be seen that seem to lead to a login service for different environments:
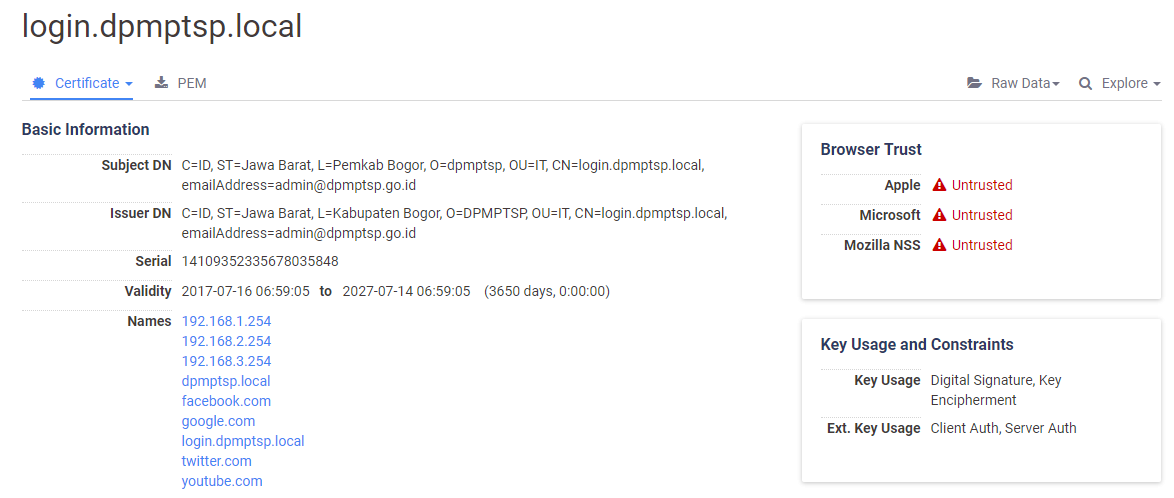
And while this is valid certificate with valid domain names, there sometimes are cases where one starts wondering what the reason was for a specific certificate. Here is an example of a certificate that very well may have been be used to decrypt traffic by impersonating SSL traffic from Facebook, Google, Twitter and YouTube:
Organization Name
If we are looking into a specific company within Censys, we can query a specific field that contains the organization’s name. Let’s say we would like to find out what certificates are registered by the Shell company. We can do a very quick query on anything that has the name Shell in it by feeding Censys the following line (or click):
parsed.subject.organization: Shell
That returns more than 4000 results, but by searching within certificates that are assigned to the domain shell.com we find that the actual organization names are a bit longer, for instance “Shell Oil Company”, or the very formal sounding (click):
(parsed.subject.organization: "Shell International Petroleum Company Limited") AND tags.raw: "unexpired"
Running that query we find a bit more than 120 certificates that were requested by that particular company name. By going over the different organizations with the name ‘Shell’ it is possible to find more businesses and domains that are leading back to this mother company. And when there are multiple companies we are interested in, we can combine them into one larger query too.
Querying on Location
Since the location of an IP address is not always accurate and a lot of websites are in the cloud, querying for certificates that were issued by a specific company in a specific city is another possibility. Here we have to be a bit more creative with our filters. Let’s say we want to query the following information:
- A business dealing with ‘finance’
- Located within New York
- Only currently active certificates
The query in Censys for that contains three parts. The first part is the word ‘finance’, followed by the operator AND to include the next part, which is the location. After that we have the last part, the previously seen ‘unexpired’ tag, that results in the following query (or click here):
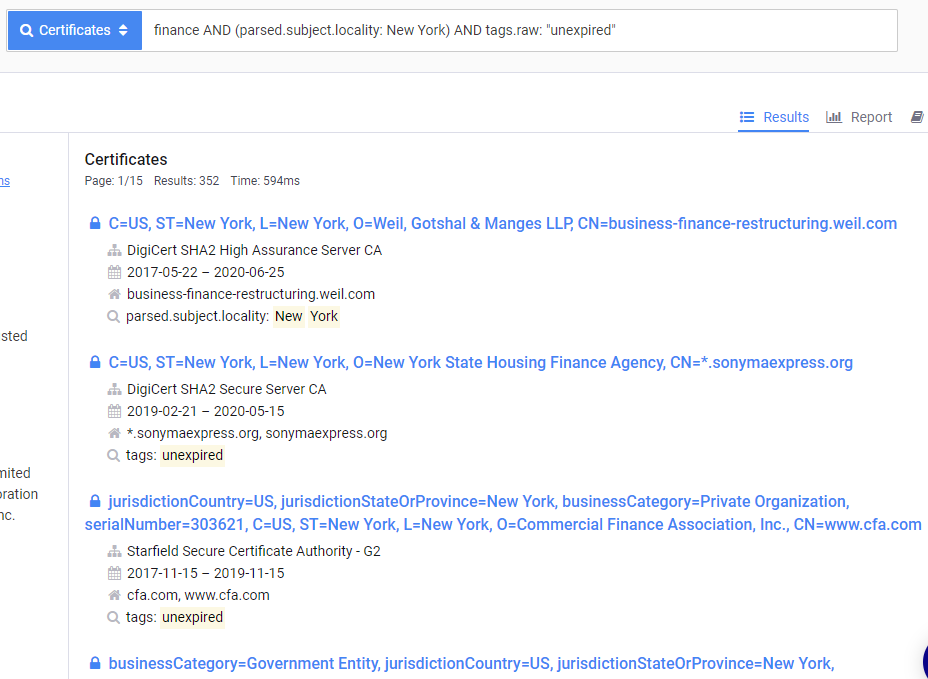
finance AND (parsed.subject.locality: New York) AND tags.raw: "unexpired"
And the result is a list of 352 certificates that are matching our query indeed show websites that are dealing with finances that are supposedly within the New York area:
More Information
Shodan and Censys can provide a lot of information when it comes to domain names and certificates. But the real strength is in the information that can be found inside them and how they are used to pivot on organizations, locations, web servers et cetera. The only thing you need is a free account on either of them. With Censys there is a limit of 250 queries a month, but that can already help you out on the first steps in this world.
For information on what fields there are within Shodan, you can visit this blog article about the features that are available. For Censys there isn’t a ready made list with fields. But Censys will help you with an auto-fill feature while you are typing, making it a bit easier to get queries right the first time.
And besides that, I was recommended the book ‘Hack The World with OSINT‘ by Chris Kubecka. I haven’t read it myself yet, but this book goes into detail when it comes to using Censys for OSINT purposes. Because there is a lot more to find out there than what is hidden in certificates.
Sector035 made a 10 Minute Tip video of this blog post’s content that can be watched below, or directly on our YouTube channel.

