If your work involves protecting organizations from social engineering attacks, you will most probably also be required to conduct open-source intelligence on the organization and its people. Your task will be to find vulnerabilities or high-risk information that is likely to be exploited by attackers in a social engineering attack. Such information would include: identifying specific technologies, key people, and their relationships with internal or external partners (typically used in spear-phishing attacks), the internal organizational culture and hierarchy, company events, and more. Your client organization will need to know which of the publicly available information pose a risk that needs to be removed or managed.
Below is a list of resources and research ideas that can be used in the OSINT phase of social engineering engagements, vulnerability assessments, or other projects. Corporate OSINT for social engineering attacks usually revolves around three main subjects: employee information or vulnerabilities (for specific persons, teams, or a broader spectrum of employees), corporate information, and the physical perimeter. The two latter tend to overlap in some instances. This blog will focus on conducting corporate research for social engineering attack simulations or vulnerability assessments.
As this is a topic that can be very broad, the list found below is not exhaustive. Some complementary information can also be found at wondersmith_rae‘s blog, found here: https://osintcurio.us/2020/03/17/corporate-reconnaissance/
Company Structure
The more information that is available about the internal company structure and hierarchy, the better social engineers are able to craft their approach. For example, conservative organizations with strong hierarchies are more vulnerable to spear-phishing or ‘vishing’ attacks involving impersonation with an authoritarian pretext. That’s because they often operate under a “do and don’t ask” culture that social engineers take advantage of. We need to be able to identify if an outsider has enough information to exploit that. Information about the target company’s internal structure can often be found in the “About Us” section of the company’s website. But if you need to get more details, look in the in Annual Reports or Corporate Governance Reports, especially if you are investigating a publicly listed company. For that, you may use Boolean searches such as:
"company name" AND "annual report“ OR "corporate governance" OR "organizational chart".
or
"organizational structure" site:company.com
The company website sometimes discloses the names and images of specific people in key positions. If not, these can also be found in the annual reports or external websites with corporate information. One example is Open Corporates. For Swiss companies, the most detailed database of companies, their people & their corporate positions is found at Money House and at Business Monitor.
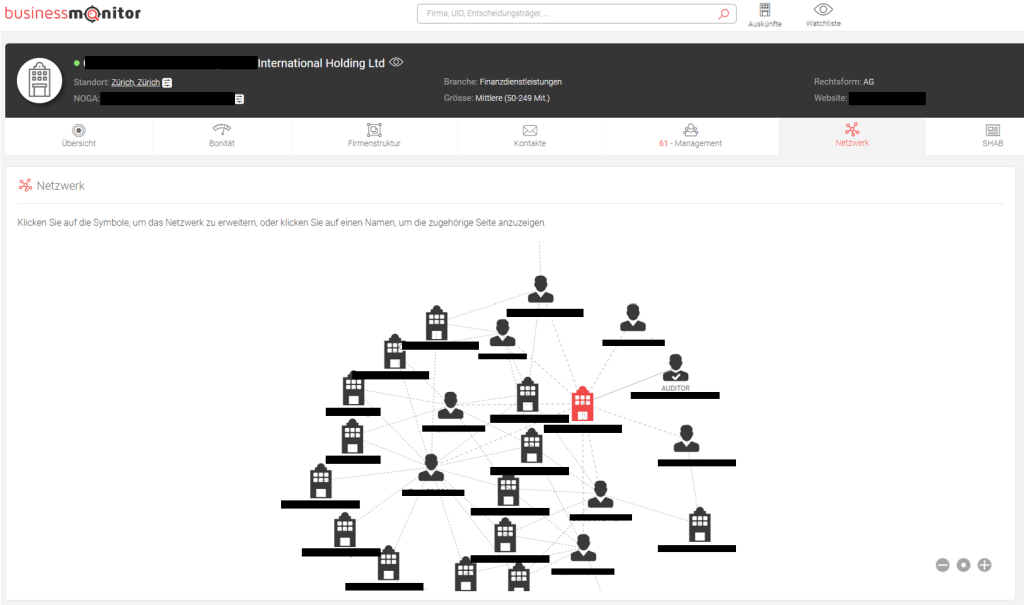
Business Monitor comes with a few extra perks, as it provides additional information such as emails, commercially registered documents & publications, and a nice network visualization between persons and other legal entities:
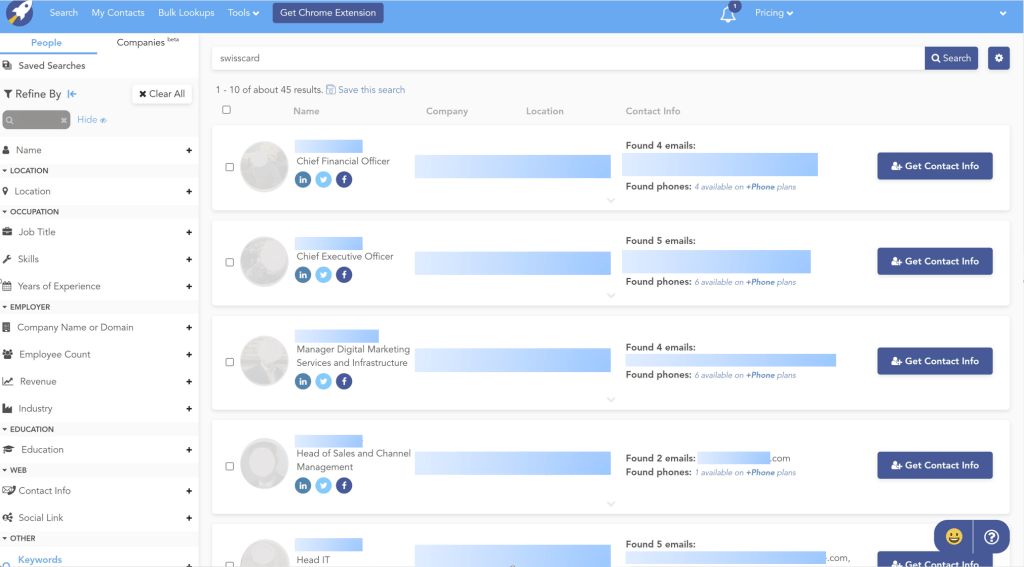
A more global option for company and employee information is RocketReach. In RocketReach, you can look for companies or specific people. It provides a variety of search options for your target (whether that is a company or person working for a company, see picture). It returns their full name, job position, potential social media accounts, company, location (particularly useful if the company has remote workers), and email addresses (professional and sometimes private ones), and phone numbers. There is, however, a caveat: you need to create an account through a business email address. Most of the information you will need is provided with the free version of your account.

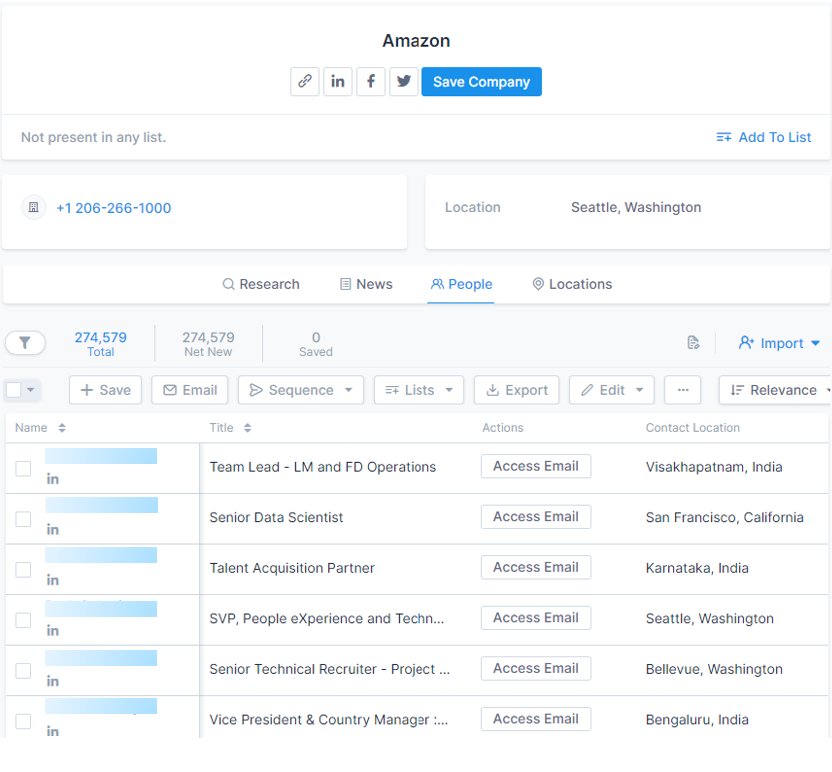
A second and similar database is Apollo. Apollo is a marketing and engagement platform with different tools used primarily for lead generation and sales. It also has a pretty rich database of companies and people. Apollo claims that their database is only sourced “from publicly available information on the internet”. It also scrapes the contents of social media accounts such as Twitter and LinkedIn. Again, there is a caveat, as you need to create an account. Most of the relevant information you will need for your OSINT objectives is free. For company searches, Apollo provides a list of company technologies, job postings, employee departments (very useful for certain social engineering pretexts), and employee lists that disclose names, job titles, locations, and emails, among other things. Amazon is used as an example in the picture below for the only reason that it is a large company that would return a lot of data in this example.
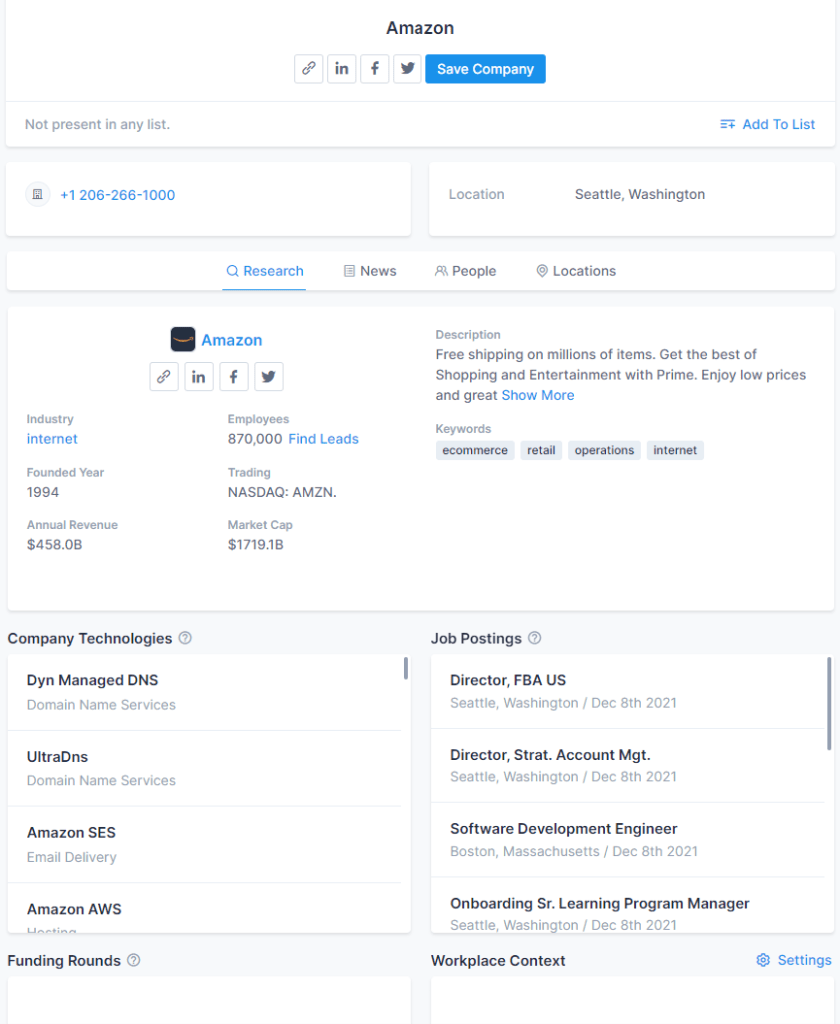
In 2018, Apollo left a database with billions of data points for companies and people publicly exposed, without a password. These are reportedly being sold in the dark web. By collecting and combining the information mentioned above, you are able to build sufficiently detailed charts of the organizational structure, certain hierarchies, and the people involved in them.
Company Culture
Not too many other resources can beat employer review websites when it comes to identifying the company culture. The three most dominant employee review websites are:
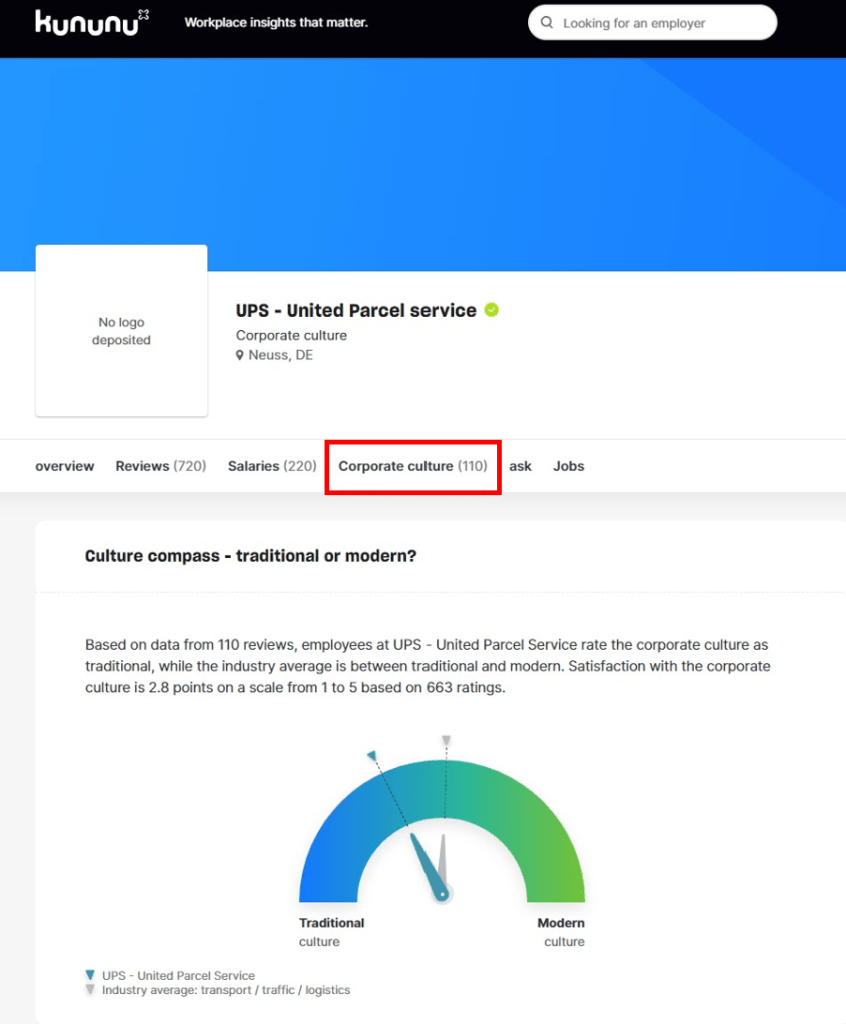
All three of them include ratings that involve the corporate culture. My favourite one, however, is Kununu. This website provides a separate page with more details on corporate culture and employee comments. The comments tend to shed a lot of light on the internal dynamics between management and employees, as well as specific details on internal processes, that slip out. This information is used by attackers that aim to imitate or include in their pretext information that is supposed to be known only to “insiders.” As mentioned earlier, an organization needs to know what information is available about them online. An organization known to have a traditional structure with strict hierarchies needs to be able to manage social engineering attacks that exploit an employee’s hesitation to report or deter suspicious activity, especially when the attackers choose to impersonate the executive management in their pretext.
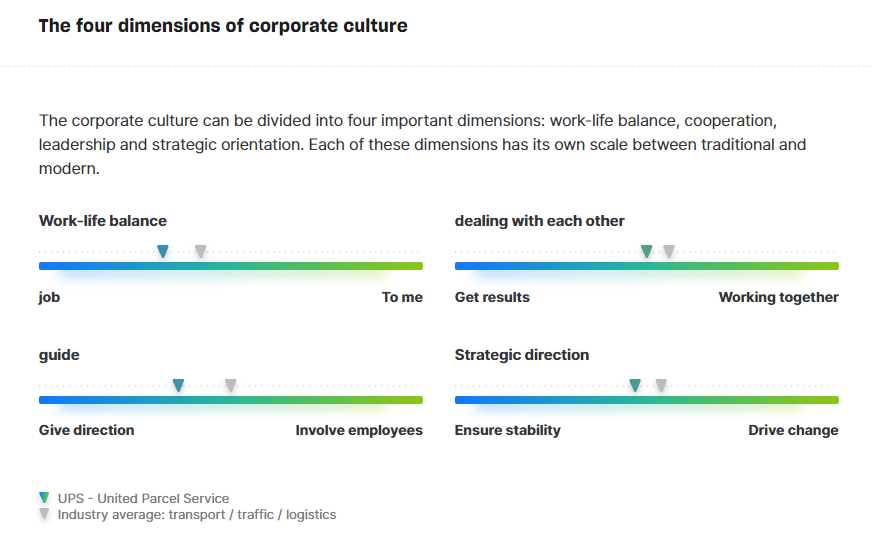
Additionally, employer review websites may provide insights into which departments are the most overwhelmed. Overwhelmed employees often choose not to exercise the required due diligence or fact-check when a request comes in), making them vulnerable to social engineering.
Service Providers
Researching the partners and service providers of the target company helps you find out whether key relationships, specific technologies, or confidential information are left exposed. There is no reason (not even a marketing one) to publish the names of specific people working on specific projects or technologies for your target company (or any company). Some partner companies or service providers may decide to publish a case study describing their work on the organization you are researching. It is not unusual to disclose too much information about the internal state of the target company and the solutions they currently provide or to identify specific names of key people in the project. Social Engineering attacks often rely on the exploitation of already existing trust relationships. By impersonating one of the people mentioned in the case study and utilizing the information provided in the rest of the document, a social engineer can create pretty convincing pretexts and (spear) phishing or ‘vishing’ attacks. Even if the information found in these case studies is not utilized for a social engineering attack, they might be researched by an attacker who tries to identify the weakest link in the target company’s supply chain or one that wants to map out the technologies the target company is using in order to craft their attack approach better. In a few of the cases I worked on, the partner company/service provider that published a case study on my target company (the client) turned out to have breached their contract by providing details on the target company’s weaknesses, old and current processes, technologies, and more. Confidential information that shouldn’t have been published was found in these documents.
To look for such documents, I use Boolean searches like this:
targetcompany AND “case study” -site:targetcompany.com
Let your imagination run free with other keywords you might need for your searches. To find service providers and partner companies in general, you may use a Boolean search such as:
targetcompany AND reference OR customers -site:targetcompany
Refine or adjust the search terms according to your needs.
Closing
The above research areas and resources are used in both vulnerability assessments and social engineering simulation attacks. No matter which of the two you conduct, you will have to inform your client company about the available and potentially exploitable information that you have found. They will be faced with a few options: eliminating it, managing it and/or developing better security awareness for their employees. The above resources are not an exhaustive list. Like mentioned at the start, we would normally also look at other corporate information, specific people, social media accounts, and physical security. But these are topics for other blog posts, another day. For now, I hope that you picked up some good tips and that you’ll use them for good! Feel free to share with us your own findings and resources.
Keep exploring, and stay curious!

