Guest blog post by Jeff Lomas (@BleuBloodHound).
There have been several excellent virtual machines (VMs) designed to assist in OSINT assessments including popular VMs such as Tsurugi Linux (OSINT and digital forensics) and Trace Labs’ OSINT VM. While these are great tools for conducting OSINT assessments it is also important to configure them to protect your host system.
What is Isolation?
Before we go down the path of configuring our systems, it is important to understand what isolation is. When we talk about virtual machines, isolation is nothing more than limiting the resources our host system provides our virtual machine. Behind the scenes, your virtualization software (VMware or VirtualBox) uses RAM, processing power, network connections, and storage you designated for your VM when you set it up. For the purposes of this discussion, we will focus on the storage made available to our VM from our host machine (we will discuss network isolation later in this post).
Why Isolate?
Depending on who/what your target is, your level of exposure to malicious files and actors will vary. Your host system could catch a nasty case of the ransomware and that will be it for the data on your host system. Now you can imagine if you were working for a large organization and your host machine was part of the network. This would be bad. It is for this reason that experts (including me) never recommend enabling shared folders between your host system and your VM. It’s off by default so it’s best to leave it that way.
VMware Workstation/Fusion
Depending on your operating system (Workstation for Windows or Fusion for Macs), there are subtle differences on how you can change your isolation options. Always remember to have your VM in a “powered off” state (as opposed to “running” or “suspended”). According to VMware’s documentation, “Enable drag and drop” and “Enable copy and paste” are enabled by default. This means we must proactively disable them if we wish to protect ourselves. For Fusion (Mac), select VM > Settings, and isolation. A special note for Fusion, VMware Tools must be installed on your VM to use these isolation features
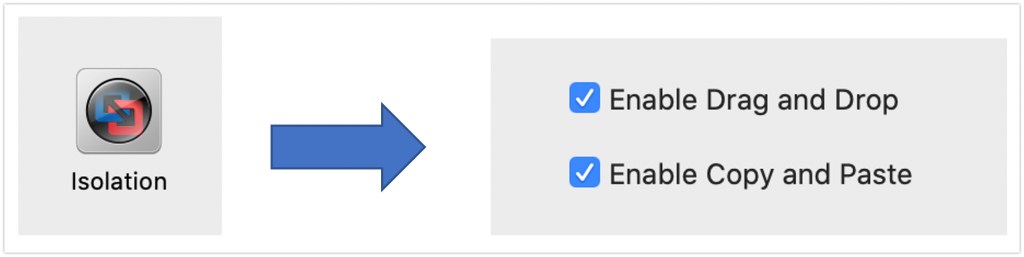
For Workstation, select VM > Settings, select the Options tab and Guest Isolation and then disable Drag and Drop and Copy and Paste. More documentation can be found at VMware’s site.
VirtualBox
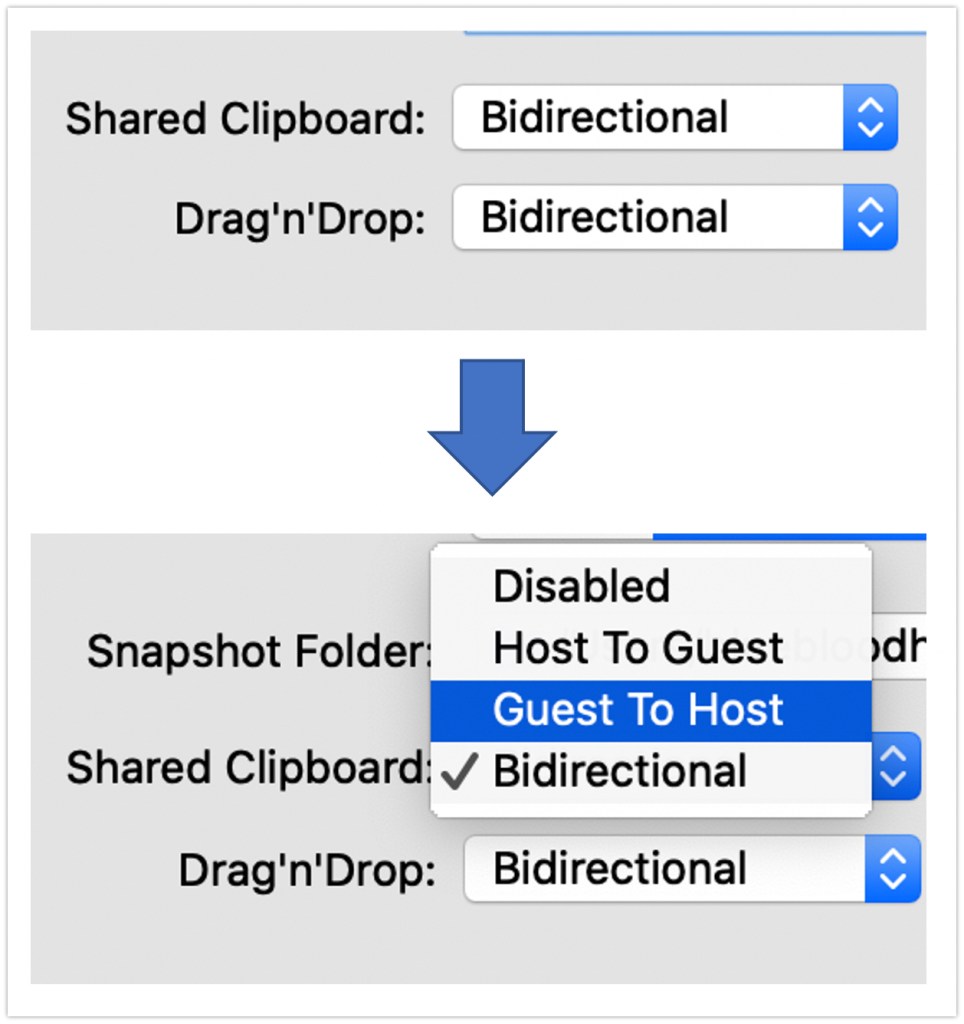
VirtualBox has increased in popularity due to the tool’s ability to not only run traditional Linux and Windows VMs, but it also supports the creation of Android mobile devices! For this reason, you may find yourself using VirtualBox in the future due to the prevalence of mobile apps and devices in OSINT assessments. VirtualBox’s setup is similar to VMware but there are some nuances. Like VMware, your VM must be in a powered off state. From the VirtualBox Manager screen, either right click on the VM of your choice or click the Settings icon then click General>Advanced Tab> “Shared Clipboard” and “Drag’n’Drop” drop down menus (shown below). You could simply disable these options or consider selecting “Host to Guest” in case you want to be able to bring items from your host system to your VM. I would caution this for the Shared Clipboard option as giving your VM access to your clipboard may be undesirable especially if dealing with malware designed to steal cryptocurrency addresses from your clipboard. If you are unsure what’s best, always default to disable.
Depending on your threat level, your organization, or the type of target you have been assessing, you may consider different ways to extract data from your VM. At a bare minimum, consider scanning all files from your assessment for malware before transferring them to another storage medium using a free tool such as Avast or Bitdefender. Consider the following methods for moving files over:
- Using an online file storage such as DropBox to copy your files to. This may or may not be allowed by your organization. For added protection in transit, zip the files and password protect them with a free tool like 7zip.
- Turn drag and drop or copy and paste back on for your virtual machine. You must shutdown your virtual machine before you can change these settings. If you want to be very careful, Lenny Zeltser has a great write-up on how to isolate a VM from your network adapter so it can’t touch the internet.
- Connect a USB device to your host machine and share it through the USB & Bluetooth device settings. This allows a connection to outside media, but not your actual host machine.

