Do you use a WiFi tether to get your laptop and other devices on the internet when there is no WiFi access point around. I’m betting many of you do. You turn on that Personal Hotspot setting on your phone and magically you have a WiFi access point for your equipment.
Would you be surprised if I told that, if you use a MiFi or WiFi tether, people are tracking your location? They are and have been since the year 2000. But before we jump to our evidence, let’s learn a bit about wireless networking, Wardriving, SSID’s, MAC addresses and hotspots.
Wireless Primer
Before we dive into the details, let’s first go over some basic terminology in regards to WiFi. Even though everybody uses it, there is more to explain than it being just a wireless network. First of all we have the network name, or SSID (Service Set identifier), that you connect to. Even though this name doesn’t have to be unique, it can sometimes reveal information about the people or company it belongs to.
Then we have the BSSID (Basic Service Set identifier) that is the MAC address of the access point. A MAC address (Media Access Control address) is a unique identifier that is used by a network device to identify itself on the underlying network. Like the SSID is used to identify itself to an end-user, the MAC address or BSSID is used by the hardware for things like routing in the rest of the network. And even though someone who connects to a WiFi hotspot doesn’t usually see that address, it is of utmost importance for your connection.
When we start a hotspot on our phone for other devices to use the same internet connection, we call that “tethering”. When you fire up your WiFi connection on your phone while being out, you will probably see examples popup like “John’s iPhone” or the default “AndroidAP“.
War Xing
Around 2000 an engineer by the name of Peter Shipley decided to map out insecure WiFi endpoints. By mounting a WiFI antenna on his car and by using a GPS receiver he was able to map out the wireless networking signals in areas fast and accurately. He coined the term Wardriving to describe this practice. Some other less known variants of mapping the geolocation of wireless networks are “Warcycling” (using a bicycle), “Warwalking” (on foot) or “Wardroning” (by using a drone).
Wigle.net
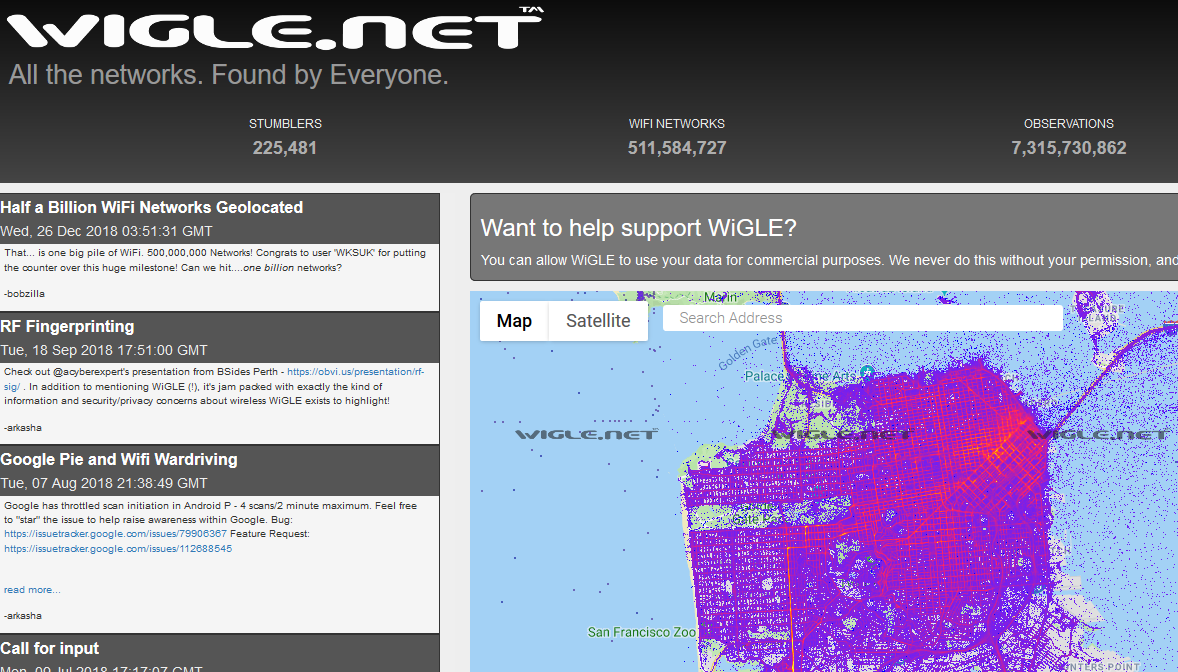
Since the early 2000s, Wigle.net has been an amazing resource to the community. It is the one-stop-shop for user-reported wireless network data. We know that others, such as Google (https://arstechnica.com/tech-policy/2010/05/google-says-wifi-data-collection-was-a-mistake/), have collected wireless network data to use in their private services (such as Google’s WiFi Location Services). Wigle.net gives us access to similar data from computer systems around the world.
Wigle.net’s data is uploaded to the site by people that collect this information on their phones, tablets, and laptops using WiFi-sniffing tools or Wigle’s own Android app. Once uploaded, users like ourselves can search and map the content and use it in our investigations
Create a Free Account
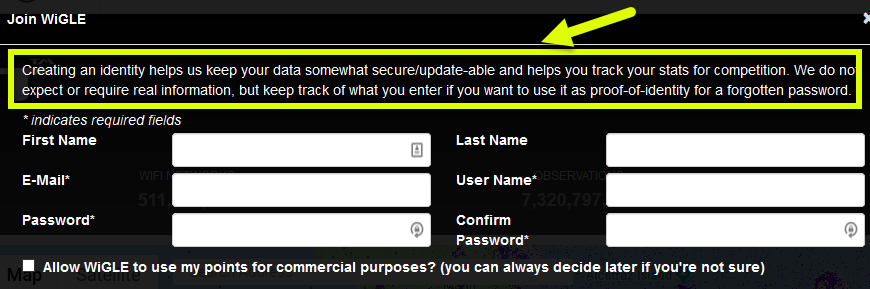
While you “can” access Wigle.net via an anonymous account, the searching features that you likely will want to use, require you to be authenticated. Their accounts are free and they note that you do not need to provide them a REAL email address, just something unique (see image below).
The Time-Traveling BSSID
For our first OSINT example, let’s head over to London, Great Britain. The De Vere Grand Connaught Rooms (61-65 Great Queen Street London, WC2B 5DA GB) conference center is where the SANS Institute has many of their London events. Know how we know this? The WiFi networks tell us!
Below is a normal Google Map of the area.

Looking at this same region in the Wigle.net site by searching for that address yields the image below.
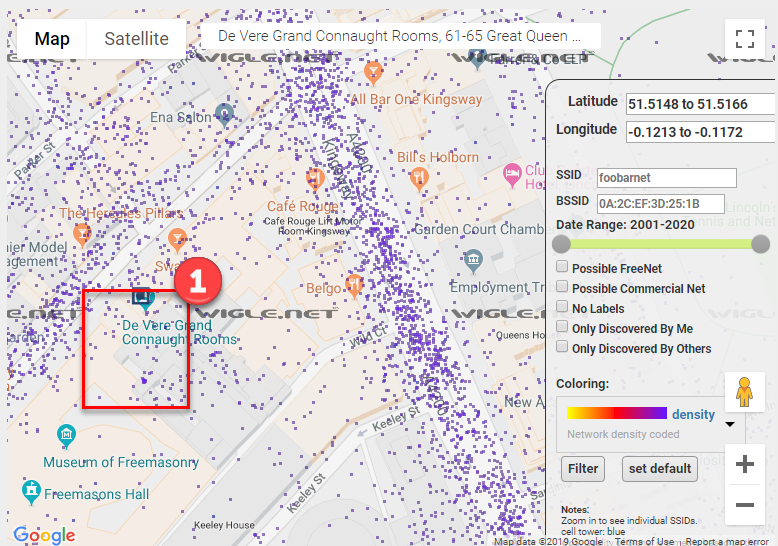
Wow! That is one BUSY-looking image. Each of those purple dots represents a wireless network that someone’s device “found” and then was uploaded to the Wigle.net site. It is common for densely-populated regions to look like this, with hundreds or thousands of WiFi networks noted within a very small region. This, of course, makes actually using this data more-challenging.
To read the information attached to each purple dot we need to zoom in. In the above image, we will zoom into the rectangle marked with a “1” on the left.
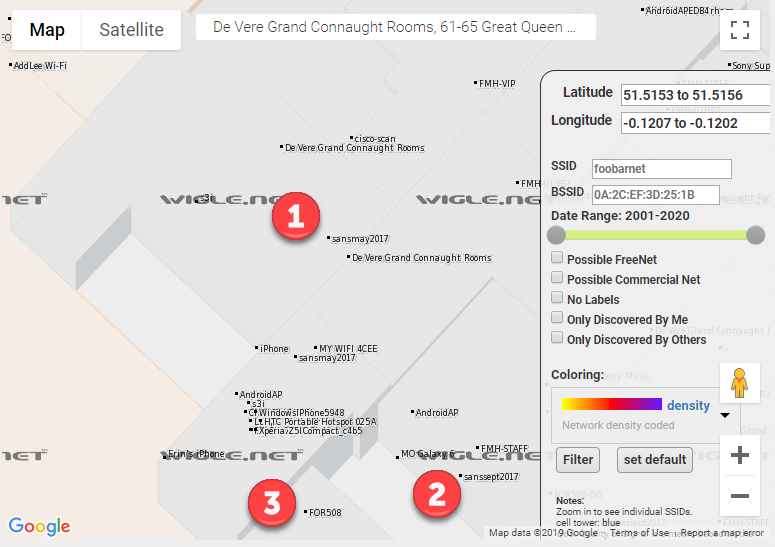
In the above map, we zoomed in a huge amount and still the font size of the Wigle.net wireless networks are tiny. We can see some interesting wireless network names at this level. Let’s examine those three points in the above image with the 1, 2, and 3 near them.
- 1 – sansmay2017 – General wireless network for the SANS training event in May 2017 at this location.
- 2 – sanssept2017 – General wireless network for the SANS training event in September 2017 at this location.
- 3 – FOR508 – Wirless network for the FOR508 SANS class when it was run at some point from this location.
From an OSINT perspective, numbers 1 and 2 above might be interesting. We have 2 wireless networks that state that they are for events across time. Here we learn both what the wireless network naming scheme is and when certain events might have been.
In OSINT, collecting data is important. Analysis of that data is essential. Let’s perform a search on the “sansmay2017” networks and see when they were discovered by the Wigle.net user that uploaded them. The https://wigle.net/search?ssid=sansmay2017 page performs the search we want and the output from that, is shown below.
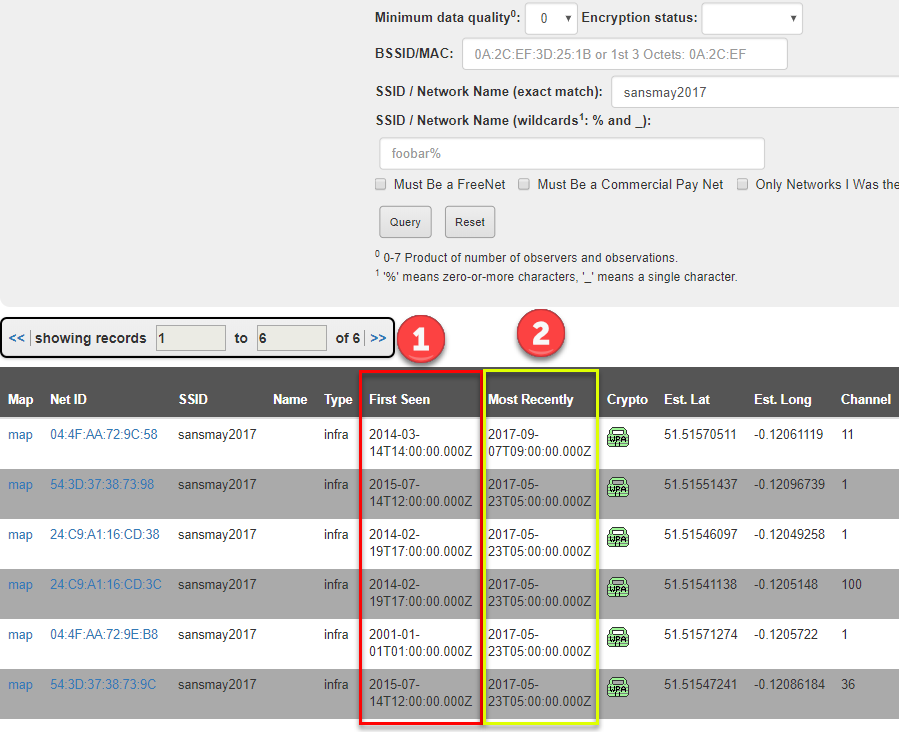
In the above image, something appears to be wrong. I mean, the access point name clearly states “sansmay2017”, right? But people discovered these WAY before May 2017 (column marked with a 1). Did they time-travel? Is something suspicious going on here? Nope. It is basic wireless networking.
What happens is that Wigle notes when the transmitter (BSSID/MAC address) for a device was first and last seen. Because the wireless network (SSID) for a device can change, cataloging a device by its BSSID, which should not change, is better since that will be unique and long-lasting.
OK, so what is going on in the image above? Chances are good that these wireless transmitters (think routers or access point devices) were used in the past and were discovered earlier than the May 2017 event. Let’s check that out by clicking on the first BSSID 04:4F:AA:72:9C:58.
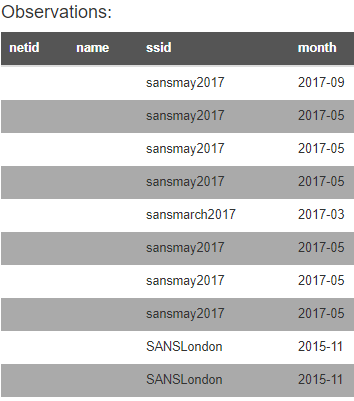
YES! We were correct! The image above shows that this transmitter (BSSID) was discovered transmitting other wireless network names before the May 2017 event.
Tracking Your iPhone
So let’s think about that last example for a moment. There was a device that transmitted a wireless networks that was noted several times in the same location. OK. Many of you carry a wireless network transmitter with you in your purse, pocket, or man-bag: your cell phone or MiFi. These devices have unique BSSIDs and, when you wirelessly tether to them, they emit an SSID that can be recorded in Wigle.
We shall pick on iPhones since they make this example simpler. When get an iPhone, you enter your first name (or a name you pick) into the device at the initial configuration. When you enable the WiFi tethering or mobile hotspot feature, the iPhone creates a wireless network with “YOURNAME’s iPhone”. If, for example, I put the name “Micah” into my new iPhone when I configured it, when I turn on the WiFi tethering, I’d expect a wireless network name (SSID) of “Micah’s iPhone”.
Now that we understand how this device works, let’s head over to Wigle.net and perform a wildcard SSID search for “‘s iphone” and see what comes back.
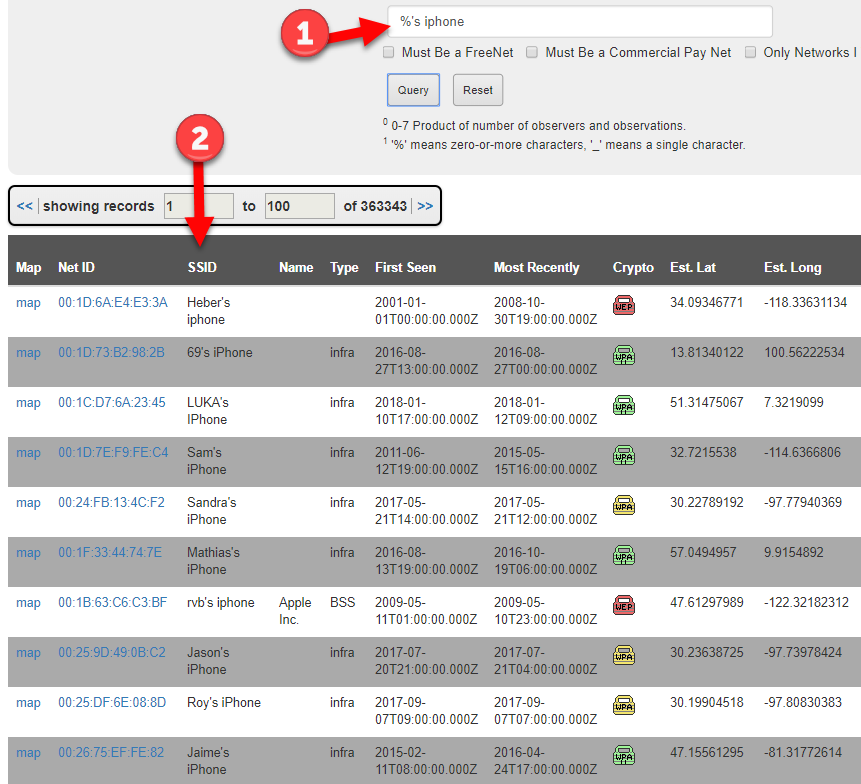
OH MY! We were WILDLY successful with that search retrieving over 363,000 entries dating back to 2001. The actual search we submitted (arrow 1 above) is “%’s iphone”, where the “%” is a wildcard telling Wigle to match to anything that comes before it.
Well this could be bad for someone’s privacy. Notice that each SSID above (arrow 2) has a geographic location where it was found. What if we pivot into one of those entries and discovered ALL the places where the wireless network was geolocated. What if it was found at:
- the device owner’s home?
- the device owner’s work?
- the device owner’s client site?
- bars, coffee shops, airports, hotels, and other places the owner might use it?
[For this next section, we are using real data from the Wigle.net site and, while it is public, we are blurring out specific details to somewhat protect the privacy of the owner of the device. On the Wigle.net site, you can see all of this data.]
We will pick a random “%’s iphone” and see if multiple locations are noted in the Wigle.net system. For the owner’s privacy, we are not going to tell you which SSID we chose, but the image below shows that, yes, yes you can find devices noted at different locations.

Since we have the latitudes and longitudes, we can use an online mapping site to plot the points. We chose the https://www.mapcustomizer.com/ site but there are many to choose from (or you can use Google Earth or another local piece of software). The image of the points plotted are shown below and clearly show groupings (marked 1 and 2) that could be home and office or coffee shop and hotel.
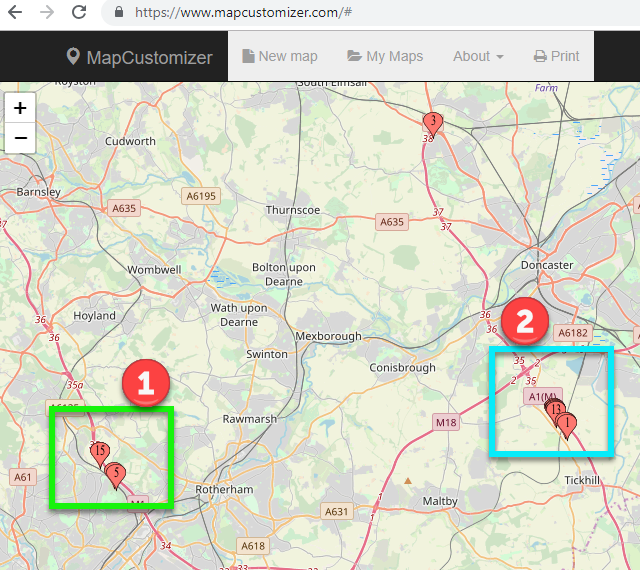
[While, in a real OSINT investigation, we would drill down into those groupings to discover what buildings, residences, and businesses are there, for the sake of the iPhone owner’s privacy, we will stop here.]
One caveat. Anyone can make their MiFi or phone or even home wireless network have the “%’s iphone” name format. Just because the wireless network name uses this format, we cannot assume that the device is, in fact, and Apple device. We can find this out using the BSSID data.
BSSID Searches for Company
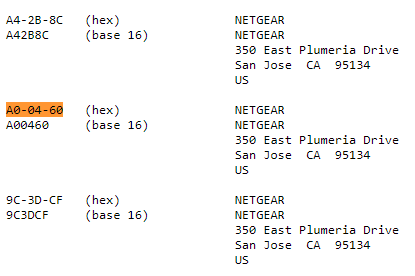
The IEEE (http://ieee.org) maintains the authoritative list of what MAC address (BSSID) is registered to what company. See, the first 6 digits in the BSSID are the company that made the transmitter or the device (it depends). We can look up this information at http://standards-oui.ieee.org/oui/oui.txt.
So if I see a device that has a BSSID of “A0:04:60:1A:33:8C”, I can search for the “A0:04:60” in the IEEE list (translate the format to use “-” instead of “:”) and find that the device owner/manufacturer is “Netgear” (see below).
Going back to verifying our Wigle.net data. Let’s look at the list of devices and the first 6 digits of their BSSIDs and look one up. Wigle.net identifies the following device as using the network name of “paolo’s iphone”. But is it an Apple device?
08:EC:A9:5B:C8:34 paolo's iphone
Let’s look up 08-EC-A9 in the IEEE list.
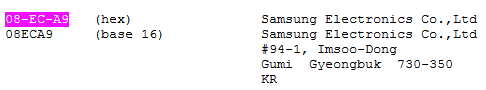
Wait a second! That is not an Apple device. That wireless transmitter is registered to the Samsung Electronics company. There are a number of reasons we might see this type of mismatch in the BSSID and network name including the device is a Samsung device and is using the “paolo’s iphone” wireless name to fool people into thinking it is an iPhone device.
Conclusions
Wireless network data and geolocation information need to be interpreted to be useful. Once again, the analysis of the data becomes important in the OSINT work. We see that wireless network information has been stored and is accessible online since 2001. Even with the uncertainties, this wireless data can be valuable in your OSINT work.
From a privacy perspective, we have some outcomes from our work here too:
- Do not use your device to wirelessly tether devices. Instead, use USB tethering.
- Understand that devices transmitting wireless signals are being recorded and cataloged and can give away locations and dates. If you have a MiFi device and travel with it, you may be providing others locations of where your device (and you) were at certain dates and times.
- Understand that the SSID name you choose can make it easier or harder to find your device(s) in Wigle.net.
- Remove your networks from the Wigle.net database (see below for details).
The folks at Wigle provide an amazing resource for WiFi mapping. They also respect the privacy of anyone who requests their information to be removed from the database as seen at the bottom of the website:
“WiGLE respects your privacy. To have records of your access point removed from our database, or if you have any questions or suggestions, send an email to: WiGLE-admin[at]WiGLE.net (please include BSSID (MAC) in removal requests).”
https://wigle.net
One other thing you can do to improve the privacy of your WiFi networks is append the tag ‘_nomap’ or ‘_optout’ to your SSID.
“WiGLE automatically hides networks (currently 16,644) with these _nomap and/or _optout tags in the ssid.”
https://wigle.net/phpbb/viewtopic.php?t=2330
Blog written by: Micah Hoffman, Sector035, baywolf88.